Discovering the Duty of Universal Cloud Storage Solutions in Information Defense and Conformity
As organizations increasingly depend on cloud storage space services to take care of and guard their data, exploring the elaborate role these services play in making certain information safety and security and meeting regulatory standards is essential. By diving right into the subtleties of universal cloud storage services, a clearer understanding of their effect on information protection and governing conformity emerges, losing light on the complexities and possibilities that exist ahead.
Relevance of Cloud Storage Services
Cloud storage services play a critical duty in modern information monitoring techniques due to their scalability, ease of access, and cost-effectiveness. Scalability is a crucial benefit of cloud storage, enabling companies to conveniently readjust their storage capability as data needs change.
Availability is another important element of cloud storage space services. By keeping data in the cloud, individuals can access their details from anywhere with an internet connection, helping with cooperation and remote job. This accessibility advertises operational efficiency and makes it possible for smooth sharing of information throughout groups and areas.
Additionally, numerous cloud storage companies offer pay-as-you-go pricing versions, permitting companies to pay only for the storage ability they make use of. In general, the significance of cloud storage space services exists in their capability to enhance data administration procedures, enhance ease of access, and lower operational costs.
Information Protection Methods With Cloud
By encrypting data before it is posted to the cloud and maintaining control over the encryption keys, organizations can stop unapproved gain access to and reduce the danger of information breaches. Multi-factor authentication, strong password policies, and regular gain access to reviews are some techniques that can improve information security in cloud storage solutions.
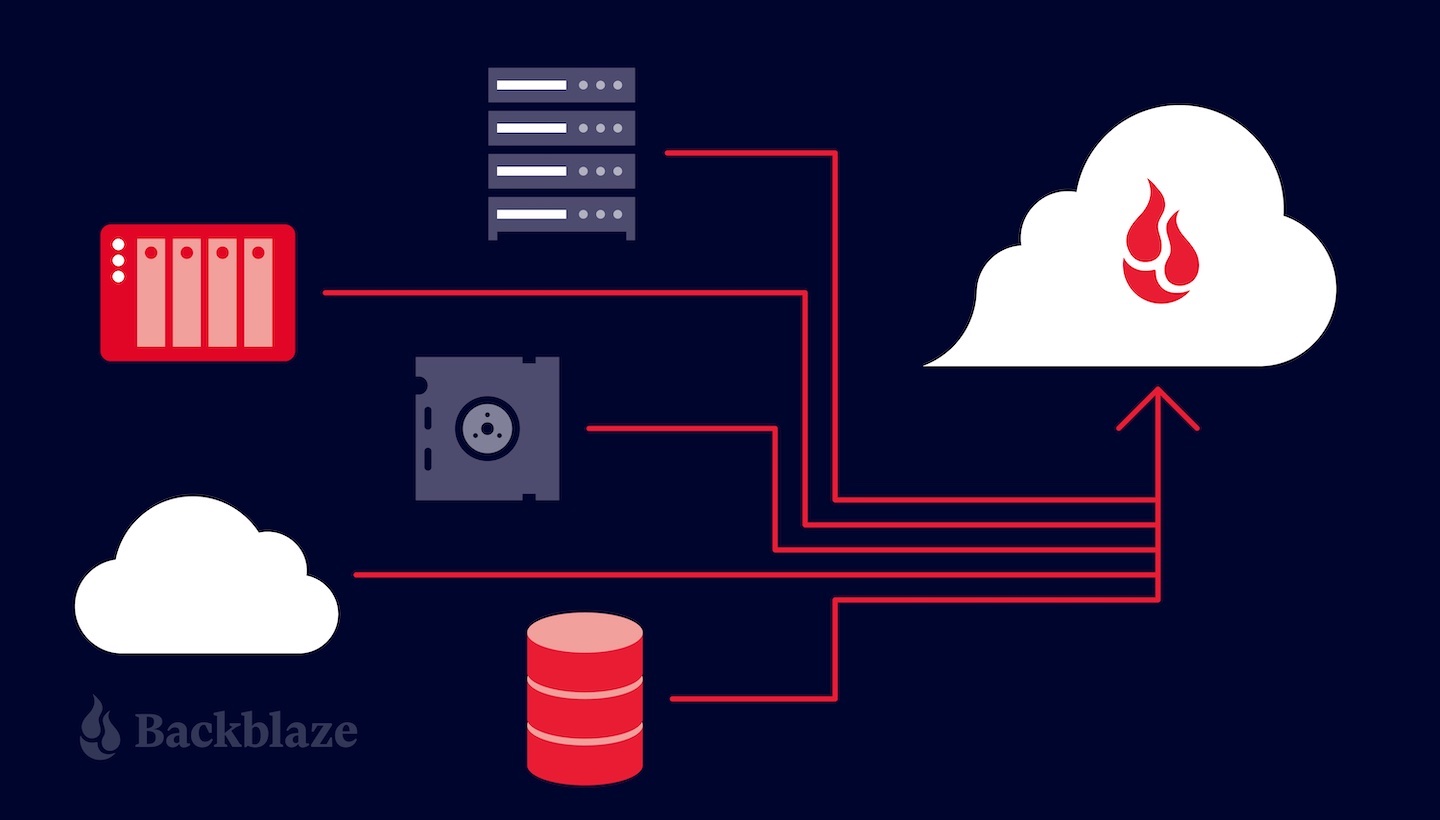
Routinely backing up information is another important facet of information protection in the cloud. By producing back-ups kept in different locations, organizations can ensure information accessibility and strength in case of unexpected occasions such as cyber-attacks, hardware failures, or natural disasters. In addition, carrying out regular security audits and evaluations can help recognize susceptabilities and ensure compliance with information defense regulations. By integrating file encryption, accessibility controls, back-ups, and regular protection evaluations, organizations can establish a robust information security strategy in cloud settings.
Conformity Considerations in Cloud Storage Space
Offered the crucial nature of information protection approaches in cloud settings, organizations need to also prioritize conformity considerations when it pertains to storing data in the cloud. Compliance needs differ across markets and regions, making it vital for companies to understand and comply with the appropriate regulations. When utilizing cloud storage space services, services need to make sure that the carrier abides by industry-specific criteria such as GDPR, HIPAA, or PCI DSS, you can look here depending on the kind of data being kept. Additionally, organizations need to take into consideration information residency needs to guarantee that data is stored in certified areas.
Challenges and Solutions in Cloud Security
Guaranteeing durable safety actions in cloud settings provides a complex obstacle for companies today. One of the key obstacles in cloud safety is information breaches. An additional challenge is the shared responsibility version in cloud computing, where both the cloud service supplier and the client are responsible for different elements of protection.

Future Fads in Cloud Information Defense
The developing landscape of cloud information protection is noted by a growing emphasis on aggressive defense strategies and adaptive protection steps (universal cloud storage). As technology breakthroughs and cyber hazards become extra advanced, organizations are progressively concentrating on predictive analytics, expert system, and artificial intelligence to boost their data protection abilities in the cloud
One of the future the original source fads in cloud data protection is the assimilation of automation and orchestration tools to streamline safety and security procedures and response processes. By automating routine tasks such as danger discovery, event feedback, and patch monitoring, organizations can enhance their overall safety stance and better protect their information in the cloud.
In addition, the adoption of a zero-trust protection model is obtaining traction in the realm of cloud data defense. This technique thinks that threats might be both outside and inner, requiring continuous authentication and permission for all users and devices accessing the cloud setting. By applying a zero-trust framework, companies can reduce the threat of data breaches and unauthorized accessibility to sensitive information saved in the cloud.
Verdict